Many organisations deploying two-way radios assume their communications are private by default. They are not. Many organisations mistakenly assume their radio systems are already secure, yet unencrypted or poorly encrypted traffic remains one of the most exploitable vulnerabilities in critical operations. From security teams at large venues to healthcare coordinators managing patient transfers, the consequences of intercepted radio traffic can be severe. This guide cuts through the confusion, explains how radio encryption actually works, and gives decision-makers a practical framework for choosing and implementing the right solution.
Table of Contents
- Why encryption is critical for two-way radios
- How two-way radio encryption works: types and standards
- Comparing encrypted radio systems: DMR, P25, and TETRA
- Deploying encrypted two-way radios: best practices
- Common pitfalls and misconceptions in radio encryption
- Upgrade your communication security with expert solutions
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Encryption is essential | Without strong encryption, two-way radio traffic can be intercepted or manipulated. |
| Choose open standards | AES-256 is the most secure choice and avoids risks of proprietary algorithms. |
| Test before rollout | Pilot testing ensures reliable coverage, security, and interoperability for your teams. |
| Update and maintain systems | Old radios or outdated firmware can expose critical vulnerabilities regardless of chosen encryption. |
Why encryption is critical for two-way radios
The assumption that radio communication is inherently private is a dangerous one. Unencrypted radio traffic is easy to intercept and manipulate using widely available, low-cost equipment. Anyone with a software-defined radio receiver and basic technical knowledge can monitor unprotected channels in real time.
The threats facing organisations that rely on two-way radios include:
- Eavesdropping: Third parties listening to operational communications, including staff locations, security codes, and patient information.
- Signal hijacking: Transmitting false instructions over an active channel to misdirect staff or create confusion during an incident.
- Social engineering: Using intercepted information to impersonate authorised personnel and gain access to restricted areas or systems.
Consider a large outdoor event where security teams coordinate crowd management over radio. If those channels are unprotected, a bad actor can monitor movements, identify gaps in coverage, and exploit them. In healthcare, intercepted ambulance communications could expose patient details and breach data protection obligations.
“Security is only as strong as the weakest point in your communication chain. If your encryption algorithm is outdated or absent, your entire operation is exposed.”
The regulatory dimension matters too. Organisations handling sensitive personal data have obligations under UK GDPR, and insecure radio communications can constitute a reportable breach. Beyond compliance, TETRA vulnerabilities have demonstrated that even encrypted radios can be cracked in under a minute when weak algorithms are in use. Understanding radio security essentials is no longer optional for sectors where communication reliability is mission-critical.
How two-way radio encryption works: types and standards
Not all encryption is equal. The term covers a wide spectrum of technologies, from basic voice scrambling to military-grade cryptographic algorithms, and the difference between them is significant in practice.
Here is a comparison of the main encryption types used in two-way radio systems:
| Encryption type | Strength | Recommended use |
|---|---|---|
| Voice inversion | Very weak | Consumer/hobbyist only |
| Rolling code | Weak | Low-risk environments |
| ARC4 | Moderate (legacy) | Not recommended for new deployments |
| DES-OFB | Moderate (legacy) | Being phased out; avoid for sensitive use |
| AES-256 | Very strong | Security, healthcare, events, public safety |
AES-256 is the gold standard; DES and ARC4 are now considered vulnerable and should not be relied upon for protecting sensitive communications. AES-256 uses a 256-bit key, making brute-force attacks computationally infeasible with current technology.
A critical point that is often overlooked is the distinction between open and proprietary encryption standards. Open standards are more trustworthy than proprietary algorithms because they are subject to independent peer review. When an algorithm is kept secret, flaws can go undetected for years, creating a false sense of security.
Sector guidance for encryption selection:
- Security and event management: AES-256 via DMR encryption is the recommended baseline.
- Healthcare: AES-256 with strict key management protocols to protect patient data.
- Construction and logistics: AES-128 or AES-256 depending on sensitivity of operational data.
- Marine and public safety: AES-256 with end-to-end encryption where available.
Pro Tip: Avoid any system that cannot clearly state which encryption algorithm it uses. Vague claims of being “digitally secure” or “scrambled” are not the same as verified AES-256 encryption.
Comparing encrypted radio systems: DMR, P25, and TETRA
With the technology explained, the next challenge is selecting the right platform. Three systems dominate the professional radio landscape in the UK and internationally: DMR, P25, and TETRA. Each has distinct strengths, weaknesses, and sector suitability.
| System | Encryption strength | Sector suitability | Key issues |
|---|---|---|---|
| DMR Tier II/III | AES-256 available | Security, events, healthcare, construction | Requires correct configuration |
| P25 Phase 1/2 | AES-256 available | Public safety, emergency services | Higher cost; interoperability complexity |
| TETRA | TEA1 to TEA3; E2EE option | Emergency services, transport | TEA1 algorithm has critical vulnerabilities |
DMR Tier II/III and P25 Phase 1/2 offer AES-256 encryption and are well-suited to security and event management operations. Both platforms support scalable deployments and interoperability across manufacturers, which is a practical advantage for organisations managing large or mixed fleets.

TETRA has long been the European standard for critical communications, particularly in emergency services. However, TETRA’s TEA1 algorithm is breakable in under a minute, and even newer end-to-end encryption implementations have exploitable weaknesses. Organisations currently relying on TETRA should review their encryption configuration urgently.
Key considerations when comparing platforms:
- DMR offers a cost-effective path to AES-256 encryption and is widely supported by manufacturers including Motorola and Kenwood.
- P25 is the preferred choice where interoperability with emergency services is required.
- TETRA remains viable with E2EE, but organisations must verify their specific algorithm and firmware version.
For organisations exploring digital trunking encryption, DMR trunking provides a scalable and secure option that balances cost with performance. When evaluating DMR vs TETRA, the encryption strength and ongoing vendor support for algorithm updates should be primary factors.
Pro Tip: Always ask your supplier to confirm the specific encryption algorithm and key length, not just the platform name. “TETRA encrypted” and “TETRA with AES-256 E2EE” are very different propositions.
Deploying encrypted two-way radios: best practices
Knowing which system to deploy is only part of the solution. The following steps ensure your encrypted radios deliver the security and reliability that those on the front line require.
- Assess your communication needs. Map out which teams communicate, what information they share, and what the consequences of interception would be. This shapes your encryption requirements.
- Shortlist compliant platforms. Based on your sector and sensitivity level, identify systems that support AES-256 and meet UK regulatory requirements for frequency licensing.
- Run a structured pilot. Pilot testing is essential to ensure interoperability and range, as formal benchmarks across environments are scarce. Test with all operational teams before committing to a full rollout.
- Train staff on encryption key handling. Encryption is only effective if keys are managed securely. Staff must understand how to handle, update, and protect encryption keys.
- Monitor compliance and update firmware regularly. Establish a schedule for firmware updates and periodic security audits.
A practical deployment checklist should include:
- Hardware compatibility with AES-256 encryption
- Frequency licensing from Ofcom where required
- Documented encryption key management procedures
- Coverage testing across all operational areas
- Interoperability testing with any partner organisations
One concern that often delays adoption is latency. In practice, AES-256 adds negligible latency of less than 300 milliseconds for real-time communication, which is imperceptible during normal operations.
For organisations upgrading mixed fleets of analogue and digital radios, a phased approach allows teams to transition without disrupting live operations. Analogue radios cannot support AES-256 encryption, so any device still operating on analogue represents a security gap that must be addressed.
Common pitfalls and misconceptions in radio encryption
Even well-intentioned deployments can fall short due to persistent misconceptions. Understanding where organisations commonly go wrong is as important as knowing what to do right.
Myth 1: All digital radios are automatically secure.
Digital transmission does not equal encryption. Many digital radios transmit in the clear unless encryption is explicitly enabled and configured. A radio described as “digital” may offer no more protection than an analogue device.
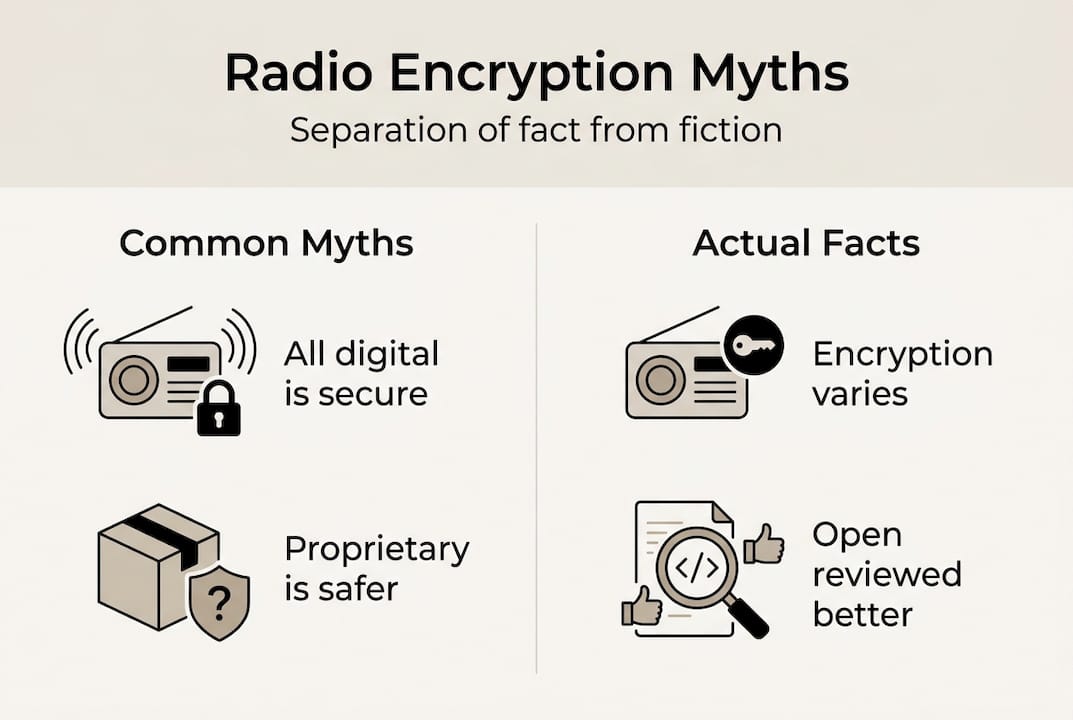
Myth 2: Proprietary encryption is safer than open standards.
Relying on secret, closed algorithms leads to security flaws, as Kerckhoffs’ principle establishes. When an algorithm cannot be independently reviewed, vulnerabilities accumulate undetected. The TETRA TEA1 situation is a direct example of this failure.
Myth 3: User errors cannot undermine encryption.
Configuration mistakes are among the most common causes of security failures. Shared encryption keys that are never rotated, radios left in unencrypted mode, and firmware that has not been updated all create exploitable gaps.
Checks every organisation should run before rollout:
- Confirm encryption is enabled on every device, not just selected units
- Verify the algorithm in use is AES-256, not a legacy standard
- Ensure encryption keys are unique to your organisation and rotated regularly
- Test that no device defaults to unencrypted mode when out of range
- Review firmware versions across the entire fleet
Pro Tip: Legacy radios are the most common weak spot in any fleet. If a device cannot be updated to support AES-256, it should be replaced rather than retained as a fallback option.
For a broader view of more radio security strategies, reviewing your full communication infrastructure alongside encryption is a sound approach.
Upgrade your communication security with expert solutions
Securing your radio communications is a practical, achievable goal with the right partner. At Smye-Rumsby, we have supported organisations across security, healthcare, event management, and construction since 1948, helping them move from general concern to effective, compliant communication systems. Whether you are weighing up hire vs purchase radios for a short-term deployment or planning a long-term fleet upgrade, our team provides consultation, pilot support, and ongoing maintenance. Explore our range of digital radio specialists solutions and browse our full portfolio of secure two-way radio products to find the right fit for your operational requirements. Contact us to arrange a tailored assessment or demonstration.
Frequently asked questions
Can encrypted two-way radios be hacked?
Yes, if weak or outdated algorithms such as TEA1 are used, but TEA1 is crackable in under a minute, whereas AES-256 remains effectively unbreakable without the correct key when properly implemented.
Does encryption slow down radio communication?
Modern encryption adds minimal delay. AES adds less than 300ms to call setup in real-world deployments, which is imperceptible during normal operations.
What is the difference between DMR, P25, and TETRA encryption?
DMR and P25 support AES-256, while TETRA’s TEA1 algorithm has known critical vulnerabilities, making algorithm verification essential before deployment.
Should I choose open standard or proprietary radio encryption?
Open standards such as AES-256 are strongly preferred because they allow independent peer review. Open cryptography standards are consistently more reliable than secrecy-based proprietary systems.
How do I pilot encrypted radios for my organisation?
Begin with a small rollout across representative operational areas, test signal coverage and interoperability with all teams, and pilot testing is essential before scaling to ensure performance meets your security requirements.

